Palo Alto firewalls have pre-defined address lists of public IP addresses with bad reputation, which are available if you have a valid threat prevention license.

There’s an issue, that these lists are not available in EDL section of configuration after initial setup of device. Therefore they couldn’t be used in security policy rules. The cause of the problem is, that the firewall doesn’t have dynamic updates for antivirus signatures yet, which include PAN EDL feeds. There’s no option to add antivirus update schedule, until you manually check for updates.

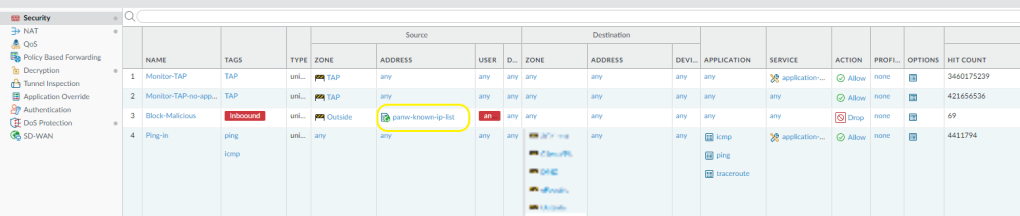
After downloading and installing the latest antivirus definition update, EDL show up and are available to use in policy rules.